Looking for the previous generation?
NoData 2025: The Ultimate Zero-Trust Data Fortress

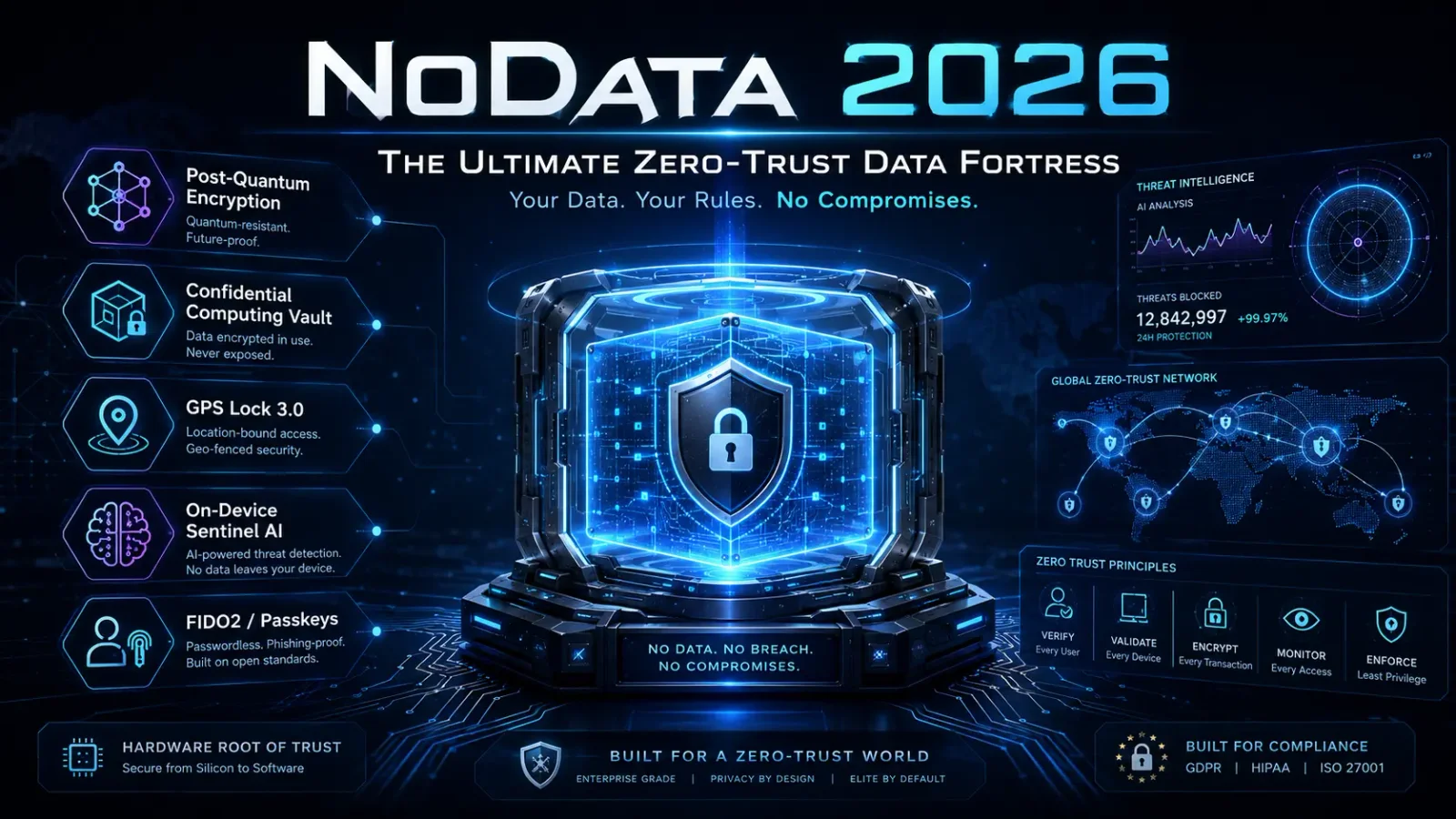
NoData 2026: The Ultimate Zero-Trust Data Fortress
Your Data. Your Rules. No Compromises.
The 2026 threat landscape isn't 2025's. Infostealer malware is now the dominant initial-access vector across documented breaches. AI-orchestrated intrusions have moved from theoretical to operational — confirmed in Dragos's analysis of the Monterrey water utility campaign, where a 17,000-line offensive framework was generated and iterated by commercial LLMs. Quantum-relevant computing milestones have continued to compress the harvest-now-decrypt-later threat window. And the OAuth graph — not the network perimeter — is now the surface area attackers actually pivot through.
NoData 2026 is engineered for this environment. Built on NIST-finalized post-quantum cryptography, hardware-rooted Trusted Execution Environments, and on-device adversarial AI detection, it delivers zero-trust, zero-exposure, and zero-compromise security for the people who can't afford a "good enough" baseline.
🔐 UNBREAKABLE ENCRYPTION — STANDARDS-BACKED POST-QUANTUM SECURITY
NoData's PQE™ (Post-Quantum Encryption Engine) has been re-engineered around the finalized NIST post-quantum cryptography standards published in August 2024 and the HQC backup KEM standardized in March 2025. No more vague "lattice-based" claims — every primitive is named, auditable, and FIPS-aligned.
✅ Hybrid AES-256-GCM-SIV + ML-KEM-1024 (FIPS 203) — Authenticated symmetric encryption combined with the standardized post-quantum key encapsulation mechanism. Resistant to both classical and Shor's-algorithm-class quantum attacks.
✅ ML-DSA-87 (FIPS 204) Digital Signatures — Post-quantum signature verification for every file operation. Forged metadata is detected before decryption is attempted.
✅ SLH-DSA (FIPS 205) Hash-Based Signatures — Stateless, conservative-assumption signing for the most sensitive vault operations, providing diversity against any future cryptanalytic break against lattice schemes.
✅ HQC Backup KEM (NIST, 2025) — Code-based cryptographic backup pathway, providing post-quantum diversity in case of future breaks against ML-KEM. NoData supports configurable hybrid modes combining ML-KEM and HQC for the most paranoid threat models.
✅ On-the-Fly Re-Encryption — Files are re-keyed on every privileged access, defeating live exfiltration attempts that rely on key persistence.
✅ Zero-Knowledge Framework — NoData servers never see plaintext, encryption keys, or recovery material. Audited annually by an independent cryptographic review board.
💡 Verifiable, standards-backed, and quantum-conservative. Specific algorithms, named parameters, FIPS-aligned implementations.
🛡️ CONFIDENTIAL COMPUTING VAULT — HARDWARE-ROOTED ISOLATION
New for 2026. NoData now executes its decryption and key-handling operations inside hardware-attested Trusted Execution Environments (TEEs), isolating sensitive material even from a compromised operating system or hypervisor.
🔹 Intel TDX, AMD SEV-SNP, and ARM CCA support across enterprise and mobile deployments
🔹 Apple Secure Enclave & Android StrongBox integration on consumer endpoints
🔹 Remote Attestation — every NoData operation can produce a cryptographic attestation proving the code that ran was the code you authorized, signed by the silicon vendor's root of trust
🔹 Memory-Safe Rust Core — the entire cryptographic engine has been rewritten in Rust, eliminating the buffer-overflow and use-after-free vulnerability classes that have historically defined endpoint security software exploits
💡 Even a fully compromised host OS cannot read your decrypted data. The TEE sees nothing it shouldn't, and proves it.
📍 GPS LOCK ENCRYPTION 3.0 — GEO-AUTHENTICATED FILE ACCESS
Now upgraded with hardware-attested location signals to defeat GPS-spoofing attacks documented across 2024-2025.
🔹 Multi-Source Location Fusion — GPS, GNSS (Galileo, GLONASS, BeiDou), Wi-Fi BSSID lattices, cellular tower triangulation, and barometric altitude are cross-correlated. Single-source spoofing fails closed.
🔹 GPS Spoofing Detection — Statistical anomaly detection on GNSS signal characteristics (carrier-to-noise ratios, satellite geometry, time-of-flight residuals) flags hostile jamming and spoofing within seconds.
🔹 Adaptive Location Entropy — Encryption keys dynamically alter if unauthorized device movement is detected, with rate-limited recovery windows to prevent timing-based attacks.
🔹 Offline Cryptographic Geo-Anchor — In no-signal zones, a previously-issued cryptographic geo-anchor permits authorized access for a configurable, time-bounded window.
💡 Your data is tied to a verified location. Spoof one signal, the others contradict it. Move the device, the keys vanish.
🏠 HOME & INFRASTRUCTURE INTEGRATION — DEFENSIVE AUTONOMY
Updated for the modern smart-home and OT environment, with Matter/Thread support and OT-aware threat correlation drawing on the lessons of recent ICS campaigns.
🔹 Matter & Thread Native Integration — Direct, encrypted control-plane integration with Matter-compliant smart-home and access-control devices
🔹 AI-Linked Alarm Response — On verified intrusion, NoData triggers data lockdown, autonomous wipe, or HoneyVault deployment — configurable per asset class
🔹 OT-Aware Threat Correlation — Enterprise deployments now correlate IT-side telemetry with OT signals (Modbus, DNP3, S7, EtherNet/IP) to detect cross-domain pivots of the type documented in the SADM/Monterrey campaign
🔹 Centralized Threat Response Module (CTRM™) v3 — Now exposes an OpenTelemetry-compliant API for SIEM/SOAR integration with Splunk, Sentinel, Chronicle, and Elastic
🔹 Rogue Device Auto-Quarantine — Zero-trust device fingerprinting blocks unrecognized hardware from accessing protected vaults
💡 If your house, office, or plant floor is breached, your data disappears before the attacker pivots.
🛡️ NO-TRACE ANTI-FORENSICS — COUNTERING STATE-LEVEL THREATS
🔹 RAM-Only Key Storage with Memory Encryption — Encryption keys live only in TEE-protected memory regions, never touching persistent storage or paged virtual memory
🔹 WORM Mode (Write Once, Read Many) — File-level immutability that survives root-level compromise; backed by cryptographic chain-of-custody for forensic counter-evidence
🔹 Cold Boot Attack Mitigation — Physical-attack countermeasures including encrypted DRAM, automatic key zeroization on lid-close events, and thermal-anomaly detection
🔹 Tamper-Resistant AI Destruction — On detected coercion or forced access:
- Crypto-Shred™ v2 — NIST SP 800-88 Rev. 1 Purge-compliant cryptographic erasure with entropy injection across all key derivation paths
- HoneyVaults v2 — Plausible decoy data archives, now generated by an on-device language model so the decoy contents are contextually realistic, not pattern-matchable
💡 Even if someone seizes your device, they'll find nothing recoverable, and possibly something convincingly misleading.
🧠 AI-POWERED THREAT INTELLIGENCE — PROACTIVE, ON-DEVICE, AND ADVERSARY-AWARE
The 2026 update of Sentinel-AI has been redesigned around two realities: most enterprise data now flows through the browser rather than traditional file pipelines, and attackers are themselves operating LLM-assisted offensive frameworks.
🔹 On-Device Local LLM — A quantized Llama-class model runs entirely on-device for behavioral anomaly detection, with no cloud dependency, no telemetry leakage, and no third-party trust assumptions
🔹 AI-Generated Tooling Detection — Heuristic and statistical signatures for AI-generated offensive tooling (the "BACKUPOSINT-class" indicators emerging from the Dragos analysis): unusually comprehensive enumeration patterns, polished-but-formulaic error handling, and characteristic over-engineering
🔹 Infostealer-Class Defense — Direct hardening against Lumma Stealer, RedLine, Vidar, and successor families: browser session-cookie protection, password-manager isolation, and clipboard-jacking defenses
🔹 Non-Human Identity Vault — Centralized monitoring and revocation surface for OAuth tokens, service-account credentials, API keys, and AI-agent credentials — directly addressing the OAuth-supply-chain attack class demonstrated by the April 2026 Vercel/Context.ai breach
🔹 Browser DLP Layer — Detects and policy-enforces against copy/paste exfiltration, AI-prompt data leakage, and unauthorized extension access — closing the gap traditional DLP suites have left open
💡 You don't react to threats. NoData stops them before they happen — without sending your behavioral data to anyone, ever.
🕶️ BLACKSITE MODE — DISAPPEARING IN DIGITAL SHADOWS
🔹 Instant Cryptographic Concealment — Files become indistinguishable from random data, defeating forensic disk-analysis tools including modern entropy-aware classifiers
🔹 Verified-Boot Wipe & Re-Provision — Securely erases and re-installs a freshly-attested OS, with cryptographic proof of the wipe for high-assurance environments
🔹 Encrypted Panic Vaults with Duress Authentication — Multiple authentication paths including duress passwords that surface decoy vaults, plausible-deniability layers, and time-locked emergency archives
🔹 Steganographic Channel Support — For the highest-risk operational profiles, encrypted payloads can be embedded in cover media for transport across hostile inspection points
💡 When stealth is survival, BlackSite Mode ensures you leave no recoverable footprints.
🚀 SEAMLESS & SECURE ACCESS CONTROL
🔹 FIDO2 / Passkey Native Support — Phishing-resistant authentication using hardware security keys (YubiKey, Titan, SoloKey) or platform passkeys (Apple, Google, Microsoft)
🔹 Biometric MFA with Liveness Detection — Fingerprint, face, retina, and voice recognition with hardware-attested liveness checks defeating deepfake and replay attacks
🔹 Zero-Knowledge Recovery Keys — Shamir's Secret Sharing across configurable trustee thresholds; only authorized recovery quorums can re-derive vault access
🔹 Quantum-Safe File Sharing — End-to-end encrypted file transfer using ML-KEM-encapsulated session keys, with verifiable post-quantum integrity attestations
💡 Phishing-resistant, biometric-strong, and quantum-conservative. Access from anywhere, with no compromise on authentication assurance.
💼 BUILT FOR CYBERSECURITY PROFESSIONALS & HIGH-SECURITY USERS
NoData 2026 is purpose-built for environments where "good enough" isn't:
✅ Cybersecurity Analysts & Red Teams — Forensic-proof data handling, attestation-backed evidence chains
✅ Executives & High-Value Targets — Industrial-espionage protection with verifiable cryptographic guarantees
✅ Military & Intelligence Operatives — FIPS-aligned post-quantum encryption with stealth and anti-coercion capabilities
✅ Whistleblowers & Investigative Journalists — Absolute privacy with plausible-deniability primitives and counter-intelligence protections
✅ Critical Infrastructure & OT Operators — IT/OT-correlated threat response addressing the AI-assisted intrusion patterns documented across 2025-2026
✅ AI Engineering & Research Teams — Non-human identity vaulting and AI-agent credential isolation, directly addressing the agentic-AI attack surface
🛠️ TECHNICAL OVERVIEW — 2026
| Feature | Specification |
|---|---|
| Symmetric Encryption | AES-256-GCM-SIV (authenticated), ChaCha20-Poly1305 (alternate) |
| Post-Quantum KEM | ML-KEM-1024 (FIPS 203), HQC backup (NIST 2025), hybrid mode |
| Post-Quantum Signatures | ML-DSA-87 (FIPS 204), SLH-DSA (FIPS 205) for high-assurance ops |
| Hardware Isolation | Intel TDX, AMD SEV-SNP, ARM CCA, Apple Secure Enclave, Android StrongBox |
| Attestation | Remote attestation via vendor root of trust; public log support |
| Memory Safety | Cryptographic core in Rust; eBPF runtime hardening on Linux |
| Geo-Security | GPS Lock 3.0 with multi-GNSS fusion and spoofing detection |
| Threat Response | On-device Llama-class LLM, OpenTelemetry-compliant CTRM™ v3 API |
| Forensic Defense | RAM-only keys with cold-boot mitigation, NIST 800-88 Crypto-Shred™ v2 |
| Anti-AI Adversary | AI-generated tooling detection, infostealer-class hardening, NHI vault |
| Access Control | FIDO2 / Passkeys, hardware security keys, liveness-verified biometrics |
| Recovery | Shamir's Secret Sharing, configurable trustee quorums |
| Supply Chain | SLSA Level 3 build provenance, Sigstore-signed artifacts, reproducible builds |
| Compliance | FIPS 203/204/205, NIS2, EU CRA, ISO 27001:2022, SOC 2 Type II |
🔒 NoData 2026 — Total Digital Immunity, Verifiable.
The 2025 release made the promises. The 2026 release shows the math, the silicon, and the standards documents behind every one of them.
💡 It's not just encryption. It's standards-backed, hardware-rooted, AI-aware digital immunity.
🚀 Available for select enterprise, government, and high-security users. Request a security review pack via the contact page.