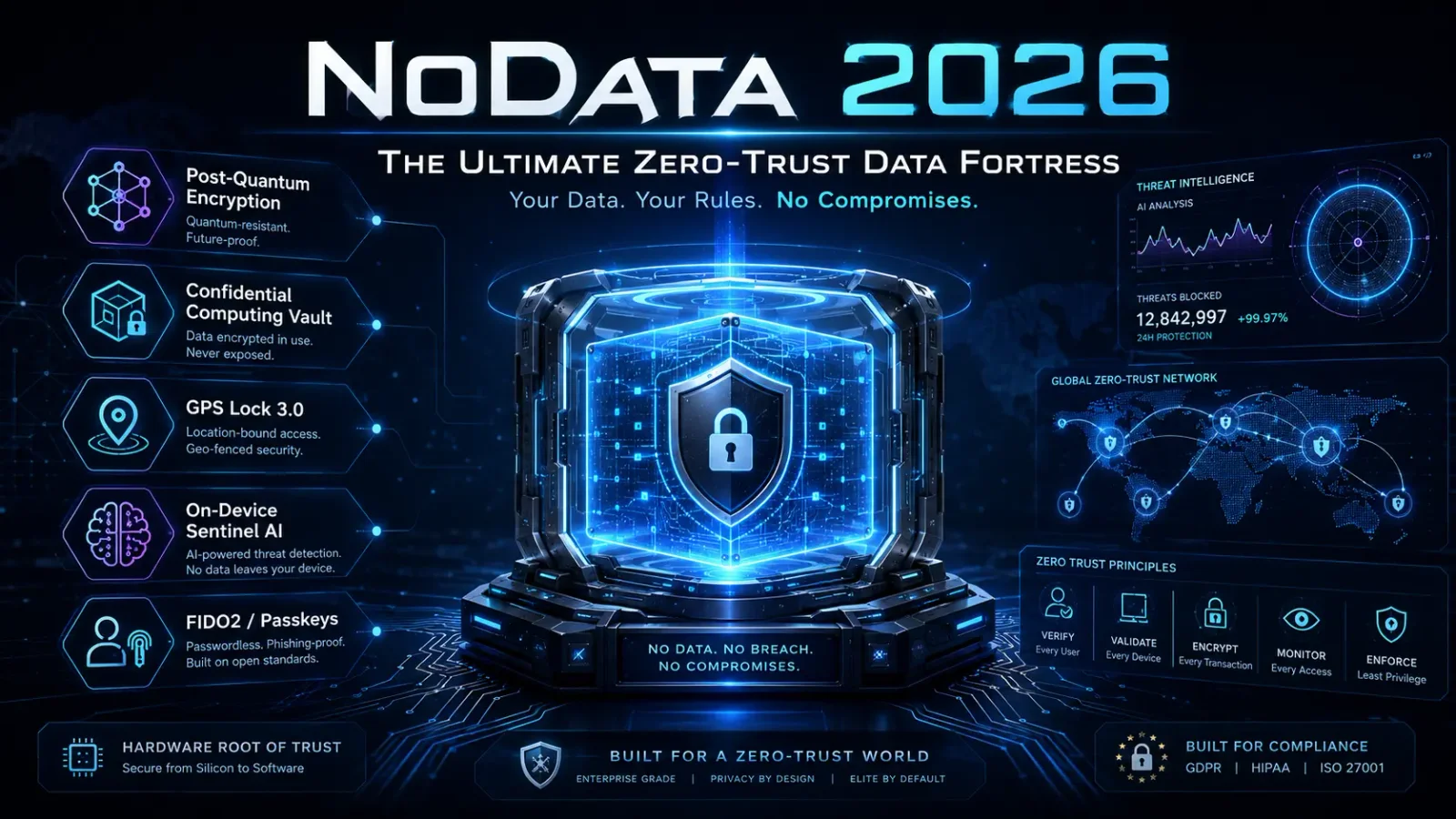
We're announcing NoData 2026 — the next major release of our high-assurance data protection platform — and we're doing it with a different posture than the launches you're used to from this space.
The 2025 release made promises. The 2026 release shows the math, the silicon, and the standards documents behind every one of them.
If you've been reading AckerWorx's coverage of the Monterrey water utility intrusion, the Vercel-Context.ai OAuth breach, and the wider 2026 supply-chain story, you already know the threat picture this product is built for. AI-orchestrated attacks against critical infrastructure are no longer theoretical. Infostealer malware is the dominant initial-access vector across documented breaches. The OAuth graph has replaced the network perimeter as the surface attackers actually pivot through. And the harvest-now-decrypt-later quantum threat is no longer a slide in a vendor deck — it's a procurement requirement.
NoData 2026 was rebuilt from the cryptographic core upward to address that environment. Here's what changed, and why it matters.
From "Trust Us" to "Here Are the FIPS Numbers"
The single biggest shift between 2025 and 2026 isn't a feature. It's a posture change. Every cryptographic claim in the new release is named, parameterised, and traceable to a published standard.
Where the 2025 release described "lattice-based cryptography," the 2026 release runs ML-KEM-1024 (FIPS 203) for key encapsulation, ML-DSA-87 (FIPS 204) for digital signatures, and SLH-DSA (FIPS 205) for the highest-assurance vault operations — all finalised by NIST in August 2024. For organisations that need post-quantum diversity against a future cryptanalytic break against lattice schemes, NoData 2026 also supports HQC as a backup KEM, standardised by NIST in March 2025, in configurable hybrid modes alongside ML-KEM.
This matters for one reason and one reason only: due diligence. A CISO procurement team can now sit down with the NoData 2026 datasheet, walk through every cryptographic primitive, and verify them against publicly-available specifications. We have stopped asking customers to trust us on the cryptography. We are asking them to verify us against the standards body.
That is the only honest way to sell security software in 2026.
Hardware-Rooted, Memory-Safe, AI-Aware
Three structural upgrades define the 2026 release:
Confidential Computing Vault. NoData's decryption and key-handling now execute inside hardware-attested Trusted Execution Environments — Intel TDX, AMD SEV-SNP, ARM CCA on enterprise platforms, and Apple Secure Enclave / Android StrongBox on mobile endpoints. Every operation can produce a remote attestation proving the code that ran was the code you authorised, signed by the silicon vendor's root of trust. A fully compromised host OS cannot read your decrypted data.
Rust Cryptographic Core. The entire crypto engine has been rewritten in Rust. Memory-safe-by-construction means the buffer-overflow and use-after-free vulnerability classes that have historically defined endpoint security software exploits are eliminated at the language level. CISA's 2024-2025 memory-safety roadmap pushed this from "good engineering practice" to "table stakes for security-critical software" — we agree.
On-Device Sentinel-AI. Behavioural anomaly detection now runs entirely on a quantised local language model. No cloud dependency. No telemetry leakage. No third-party trust assumptions. The same model surface also powers the new AI-generated tooling detection layer, which heuristically identifies the characteristic fingerprints of LLM-assisted offensive frameworks of the type Dragos documented in the Monterrey campaign.
New Defences for 2026's Actual Threats
Three new feature categories were added specifically because 2025-2026 threat data demanded them:
Infostealer-Class Hardening. Lumma Stealer, RedLine, Vidar, and successor families have become the credential-acquisition pipeline of choice across the criminal ecosystem. NoData 2026 adds direct, targeted defences: browser session-cookie isolation, password-manager containerisation, and clipboard-jacking countermeasures.
Non-Human Identity Vault. OAuth tokens, service-account credentials, API keys, and AI-agent credentials are now monitored, audited, and revocable through a single surface — directly addressing the OAuth-supply-chain attack class demonstrated by the April 2026 Vercel/Context.ai breach. If you can't enumerate every OAuth grant authorised against your tenant in under a minute, you need this.
Browser DLP Layer. Traditional DLP suites do not see what happens inside the browser tab. Copy/paste exfiltration, AI-prompt data leakage, and rogue extension access have therefore become an enterprise-grade gap, as Keep Aware's research highlighted earlier this month. NoData 2026 closes it with policy-enforced detection at the browser layer itself.
Updated Geo-Lock, Updated Anti-Forensics
GPS Lock 3.0 addresses the GPS-spoofing attacks that became affordable in 2024-2025. Multi-GNSS fusion across GPS, Galileo, GLONASS, and BeiDou — combined with Wi-Fi BSSID lattice cross-correlation, cellular triangulation, and barometric altitude — means single-source spoofing fails closed. Statistical anomaly detection on signal characteristics catches active jamming and replay attempts within seconds.
Crypto-Shred™ v2 is now NIST SP 800-88 Rev. 1 Purge-compliant, with entropy injection across all key derivation paths. HoneyVaults v2 generate decoy contents using an on-device language model, so the plausible-but-fake archives are contextually realistic rather than pattern-matchable by a sufficiently competent forensic analyst.
Who This Is Built For
NoData 2026 is purpose-built for environments where "good enough" isn't:
Cybersecurity analysts and red teams handling forensically sensitive material
Executives and high-value targets at credible risk of industrial espionage
Military and intelligence operatives requiring FIPS-aligned post-quantum encryption with stealth and anti-coercion capabilities
Whistleblowers and investigative journalists working in adversarial environments
Critical infrastructure and OT operators facing the AI-assisted intrusion patterns documented across 2025-2026
AI engineering and research teams managing the agentic-AI credential and non-human-identity attack surface
If you're none of those things, NoData 2026 is overkill for your threat model — and we'll happily tell you that on a sales call.
Availability
NoData 2026 is available now to qualified enterprise, government, and high-security users. Standard procurement-due-diligence material is available on request, including the full cryptographic specification, build-provenance attestation (SLSA Level 3, Sigstore-signed artifacts, reproducible builds), and the independent cryptographic review board's annual audit summary.
For technical pre-sales conversations, security architect briefings, or compliance documentation packs (FIPS 203/204/205, NIS2, EU CRA, ISO 27001:2022, SOC 2 Type II), reach out via the contact page or email the team directly.
The 2025 release earned us our reputation. The 2026 release proves it with paperwork.
NoData is developed under the AckerWorx group. Editorial coverage of NoData on AckerWorx is written to the same standards as our independent threat analysis — if a feature claim doesn't survive technical review, it doesn't ship in either the product or the article.